As much as I love to call out a vendor on marketing nonsense, Ramesh Prabagaran, Director of Product Management at Cisco, made some compelling marketing statements about SD-WAN at Networking Field Day 19. In particular he said:
- Over the next two years, 90% of enterprises will be making a decision about SD-WAN.
- SD-WAN has become a conversation about on-ramping into the cloud.
- SD-WAN can provide security advantages because of how it can provide WAN segmentation.
- The WAN is the business critical connecting fabric of our networks.
SD-WAN has been around for some time, and I believe its value to networking has been well-established. However, Cisco hasn’t been a big part of the SD-WAN story until recently.
Cisco IWAN was interesting, but some would argue that it isn’t SD-WAN. Cisco’s acquisition of Viptela implies they knew this, and in 2017 they purchased what many consider to be the leading SD-WAN vendor at that time. This means Cisco now has the opportunity to lead the SD-WAN market which is already past early adoption and well underway to mass adoption.
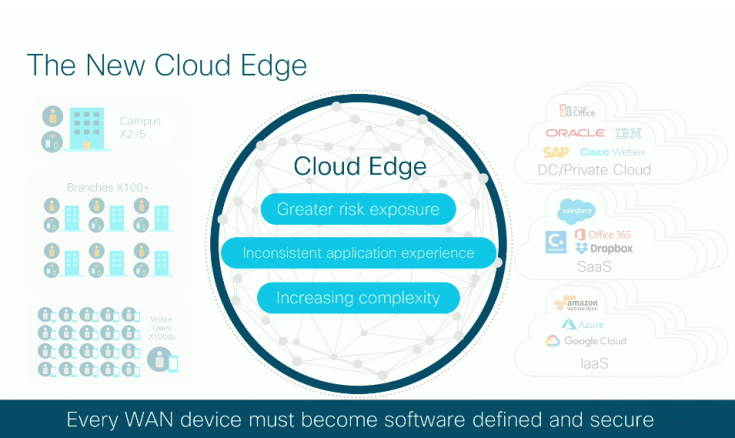
Cisco defines this path to mass adoption in terms of cloud adoption.

Cloud adoption requires easy branch connectivity, demands new security requirements, and requires LAN-like connectivity over the public internet. At Networking Field Day 19, this theme was clear theme to me. Yes, David Klebanov explained the nuts and bolts, and Kureli Sankar focused on SD-WAN security, but the overall theme was how to on-ramp to and manage a multi-cloud topology.
Multicloud refers to the use of multiple cloud service providers, but it’s important to remember that most organizations still maintain local resources in their own data centers, too. Therefore, multicloud also refers to local private clouds working seamlessly with their public cloud counterparts such as AWS, Azure, Office 365, etc.
Several of the problems with a multicloud environment are:
- Ensuring a high quality user experience
- Migrating branches to cloud connectivity
- Dealing with new security risks
User Experience
There are several dozen SD-WAN vendors out there using similar technologies to provide resilient and high quality WAN connectivity. SD-WAN is proven technology, in my opinion.The technology makes use of path probes, cloud gateways, proprietary control-plane protocols, etc in order to provide a high quality experience for end-users even over an aggregate of public internet links.
Migration
But practically speaking, how do organizations migrate an entire infrastructure to a software-defined WAN? Doing a one-for-one replacement of branch routers might be possible in a small organization, but it would take months or years for larger organizations to upgrade their entire WAN that way.

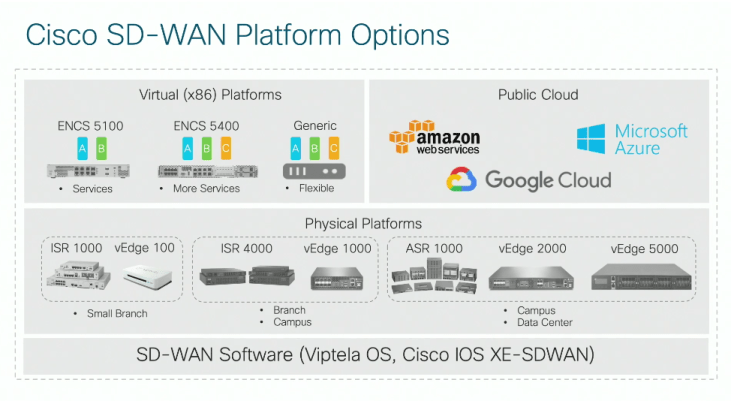
Cisco has two methods for deploying an SD-WAN. The first is to deploy one of the Viptela vEdge appliances in each branch and manage the entire infrastructure with vManage. This might work in some scenarios, but it doesn’t solve the problem large organizations have migrating to an SD-WAN quickly and easily.
The second option is to upgrade the code on existing branch Cisco ISR routers to the latest version of IOS-XE SDWAN software enabling SD-WAN features on an ISR already in the rack. The IOS-XE SDWAN code converts the router to an SD-WAN appliance managed by vManage, and though this still requires significant planning and time to deploy across a large organization, it’s a faster and much more viable option for companies who already run ISRs.
As of November 2018, about 75% of the Viptela code was embedded in the IOS-XE SDWAN image with plans to bring that to 100% feature parity in the coming months. We lose a few features that become irrelevant, such as various IP VPN services, but if you’re running an SD-WAN, technologies like DMVPN are completely unnecessary anyway.
Migrating to the IOS-XE SDWAN code is a matter of uploading the image to the router and booting the device to the new code. This something most network admins are already familiar with, so the workflow to migrate should be easy. The actual code is supported a pretty wide variety of modern ISR models including the CSR virtual router.
After upgrading the code, the new control plane stack comes online which speaks OMP to the various controllers and NETCONF to the vManage system. There is no interoperability problem on the WAN side; the only real interoperability needs to happen southbound with other existing devices behind the upgraded router.
There’s also a configuration migration tool which requires only that you paste a router’s current config into vManage. vManage flags incompatible lines of config for removal, then during upgrade, the tool/vManage reaches out to router via API calls to pull in configuration and create the corresponding vManage templates.
I want to mention that though the migration is simple for experienced network teams, they would still have to learn a new platform, the vManage network management system. That part is unavoidable, but at least some of the migration pain can be mitigated.
Mitigating Security Risks
Moving to an SD-WAN for mutlicloud environments exposes security risks.
Traditionally, branch traffic destined for the public internet would be backhauled to a data center where firewalls, URL filtering and IPS devices would inspect traffic. In an SD-WAN, traffic destined for AWS, Azure, GPC, etc, is sent directly to the cloud service provider from the branch. This means security needs to happen at the branch level.
Cisco solved this problem by integrating components of Firepower Threat Defense, or FTD, to each SD-WAN appliance. Existing inside a container in the IOS-XE SDWAN code are many of the FirePOWER features we use today with FTD appliances and service modules on ASA firewalls.

The device is application aware, recognizing over 1400 applications, and is built on Snort with the ability to filter about 80 URL categories. This means at the branch level we can have WAN segmentation of applications – something difficult to do even at the main office/data center level.
Is Cisco The Future of SD-WAN?
I’m pretty sure SD-WAN is going to be the standard for many enterprise WANs. I don’t mean that all other technologies will be going away, but for the traditional multi-site organization, the reasons to migrate to an SD-WAN are very compelling.
The question is, will Cisco, who has until now been dominant in most areas of networking, be the dominant player in the SD-WAN space?
Certainly the acquisition of Viptela secured Cisco a spot as contender. Though they are still selling the old Viptela appliances, the decision to create a new IOS-XE SDWAN code that can be used on existing Cisco routers completely secures Cisco as a leader in this space. There are at least a million ISRs out there managed by organizations that already know Cisco: they have a supply chain, they know the support methods, they know their local account managers and their children’s names.
The process to lab a few ISRs a company already owns and then deploy en masse to branches is much easier than purchasing dozens or hundreds of new physical appliances. This makes on-boarding to a multicloud environment much easier, faster, and potentially cheaper depending on licensing costs.
The goal for many organizations in 2019, including small organizations, is how to utilize cloud services in a hurry. SD-WAN will inevitably be part of those conversations, and Cisco, through the Viptela acquisition and especially because of the IOS-XE SDWAN software on ISR routers, will likely be at the forefront of many of those conversations.
Thanks,
Phil

