Leaf-spine is the default. But it’s not always the right answer.
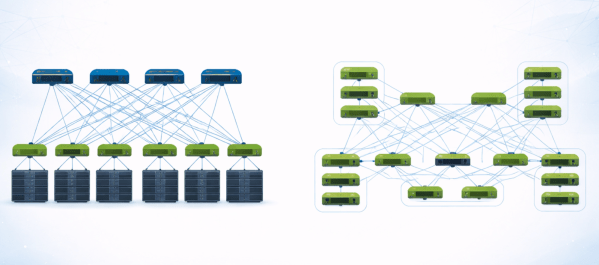
In modern data center networking, the leaf-spine Clos fabric has become the default architecture for good reason. It’s predictable, scalable, and aligns well with familiar Ethernet-based designs and operational models. But as workloads evolve, particularly with the rise of large-scale AI and distributed systems, alternative topologies like butterfly fabrics are getting renewed attention. Both architectures aim to deliver high bandwidth, low latency, and scale, but they approach the problem in fundamentally different ways.
Continue reading “Choosing Between Leaf-Spine and Butterfly Fabrics in Modern Data Centers”