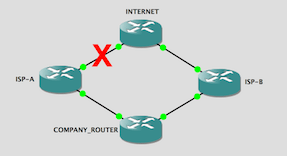
Sometimes political, financial, or logistical hurdles determine how we solve networking problems. In these tricky situations we may not be able to solve the problem the way we’d prefer, but we still need to solve the problem.
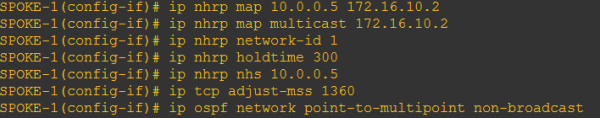
In this post I’m going to look at how we can solve a WAN failover scenario when we have a default route learned from both of our service providers and a reachability problem via our primary ISP.
Continue reading “BGP Default Route Failover Using Reachability”









 We don’t think in five paragraph essays. At least I don’t. We think in small explosions of ideas in a nebulous, non-linear cloud of word pictures. It makes sense in our own minds, but try to communicate those ideas to someone else, and we find that sometimes we don’t have as clear a picture of our own ideas as we thought we did.
We don’t think in five paragraph essays. At least I don’t. We think in small explosions of ideas in a nebulous, non-linear cloud of word pictures. It makes sense in our own minds, but try to communicate those ideas to someone else, and we find that sometimes we don’t have as clear a picture of our own ideas as we thought we did.