There’s a new story being told in the networking industry. The CCIE isn’t what it used to be, and pursuing it doesn’t make as much sense as in years past. My initial response to this is simple: BALONEY.
Network Automation: Another Tool in the Toolbox
Over the last few weeks I’ve noticed a few tweets and blog posts regarding the immaturity of network automation methods and the danger in utilizing those methods in production networks. Though I agree that processes always have room to mature and that wiggling wires in a production environment always poses some risk, I believe this new emerging narrative in social media makes several assumptions that aren’t necessarily true.
Continue reading “Network Automation: Another Tool in the Toolbox”
School’s Out For Summer
School’s out, but I can’t wait for the fall semester to start. I don’t even know what class I’ll be teaching, but I know it’ll be awesome, and it’s going to be the best class I’ve ever had.
How do I know this? A few reasons, actually.
The Joy of Just Getting the Job Done
Getting the job done, whether blog-worthy or not, always gave me a deep sense of accomplishment in my work. Besides, it’s always the junior engineers cutting over IDFs in the middle of the night that get to expense all the pizza they want.
Your wired LAN is dumb…or at least it should be
Why aren’t our wired LANs more like WLANs? Wireless vendors have already been doing for years what switch manufacturers are only starting to get into in the last couple years. A rough comparison of a few attributes of typical wired and wireless networks shows striking differences in how we manage our LANs and WLANs.
Continue reading “Your wired LAN is dumb…or at least it should be”
Fate Sharing in the Network Core
Network engineers like redundancy. It’s not that we just want double of everything – we want the networks we design and manage to be super fast, super smart, and super resilient. In the LAN and in the data center we’ve been logically joining network switches using technologies such as Cisco StackWise, the Virtual Switching System and Virtual Port Channels with fabric extenders in order to consolidate control and data plane activities and provide greater fault tolerance, easier management and multichassis etherchannel for path redundancy. These are great benefits, but they can be reaped only by proper design. Otherwise, an engineer may introduce more risk into the network rather than make it more resilient.
Teach Something
I can’t help myself. Even though I couldn’t wait to get out of a teaching career in my mid/late 20s, I still teach a class every semester at a local community college. I don’t plan to ever stop.
How Rightsizing A Network Saved Millions
For those of us in the trenches, for those of us designing networks, for those of us configuring hardware and writing proposals for the next fiscal cycle: it’s time we start to take rightsizing the network more seriously. Read the rest of the article at the Packet Pushers website.
Amidst discussion of SDN ambiguity at Networking Field Day 11, SD-WAN stood apart as something we understood, and I think that’s because we understood its use case very well.
Continue reading “SD-WAN with Silver Peak: The Business Use Case”
Information Security: Something Doesn’t Add Up
My experience leads me to think that information security is, in actual practice, more a matter of reacting to something bad that happened in the news shaking up the C-level enough to do something. But I don’t think the solemn promises of tighter security and subsequent actions match up. I may not be able to spot a tell like Patrick Jane, but something doesn’t seem right.
Continue reading “Information Security: Something Doesn’t Add Up”
Short and Sweet Cisco VSS
This post is a short, sweet and to the point copy/paste resource for configuring Cisco’s Virtual Switching System.
We Work with People Just as Much as we Work with Packets
Being a good network engineer requires a strong technical skill set. In fact there’s an entire industry devoted to technical training in networking technologies. We know that persistent technical training is necessary to keep pace with constant changes in technology, so I’m sure we agree that technical proficiency is important for the network engineer. If you don’t have a deep understanding of how VPN technology works, you’ll have a very difficult time troubleshooting a site-to-site VPN without the help of some [unnamed] technical assistance center. But is that all that’s required for a successful career in networking?
Continue reading “We Work with People Just as Much as we Work with Packets”
I Still Go To School Every Day, But Now I Call it Professional Development
Few fields require the continual professional development that IT does, but few fields offer the incredible rewards that a commitment to developing the skills of our trade can provide. Many factors come together to shape if, why, and how we advance in our field, and though I can speak only of my own experience, I believe the lessons I’ve learned from my journey so far may be of some value to others also on a similar path.
Continue reading “I Still Go To School Every Day, But Now I Call it Professional Development”
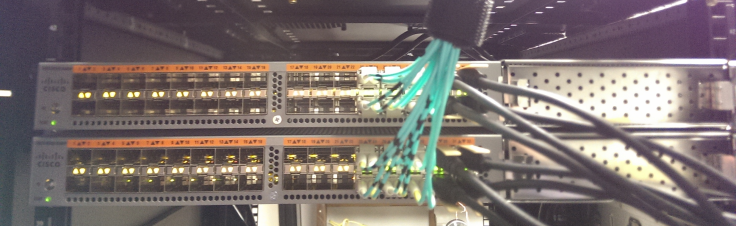
Cisco Nexus Switches Part 2: Basic Configuration
This week’s post will cover basic information gathering and configuration of Cisco Nexus switches. I’ll be using the 5500 series as my example and covering the basics without getting into features such as fibre channel, VSANs and that sort of thing.
Continue reading “Cisco Nexus Switches Part 2: Basic Configuration”
Cisco Nexus Switches Part 1: A Brief Overview
A brief overview of Cisco Nexus switches.
Continue reading “Cisco Nexus Switches Part 1: A Brief Overview”
Why Buy One When You Can Buy Two For Twice the Price
I get pretty excited when new network gear shows up at the loading dock. I get psyched when I get to configure an interesting technology that I rarely get to use. But considering our responsibility to our customer or employer, sometimes we need to put that aside in favor of the simpler (or cheaper) but more appropriate solution. Let me give you one example.
Continue reading “Why Buy One When You Can Buy Two For Twice the Price”
Don’t Forget the Plugs
How many times has one of your network projects come to a screeching halt (probably at 2am) because you didn’t have the right power plug or patch connector? Seems like such a trivial thing, but millions of dollars of equipment won’t do much more than look pretty in the racks until it’s all powered up and connected together.